Dejpaad Network Engineering & Security
Comprehensive Cybersecurity Solutions for Your Business's Protection
Since 2013, Dejpaad has established its position as a leading, committed, and professional company in the field of security and network infrastructure to accompany any organizations, government institutions, and the private sector.
By obtaining the licenses and certificates of the Supreme Council of ICT of Iran, the Tehran ICT Guild organization, the AFTA, and the SAMTA, and receiving the rank 1 of the IT companies, Dejpaad has proven its competence to implement projects in any complexity and on any scale.
- Organizations, regardless of size, are always mindful of safeguarding their assets. Securing their data and network is crucial for taking stronger strides forward. Dejpaad paves the secure path for your organization's development.
Dejpaad specializes in offering a wide range of
Hardware and Software products
In today’s world, data is considered the most valuable asset, and the use of innovative and up-to-date technology is what sets any organization apart. Dejpaad Company excels in this by accurately identifying market needs and staying current with the latest technology trends. As a result, they offer a diverse range of networking and network security products from some of the most reputable global brands.
Computing devices
Servers function as the core of contemporary networking infrastructure, furnishing vital services, security, and scalability crucial for business and organizational functionality. Through server utilization, entities can boost their competitive edge, streamline operations, and offer top-notch services to their clientele, thereby enhancing overall performance and effectiveness.
Storage Devices
Given the scale of network infrastructure and the amount of data produced by users, a variety of solutions are considered for storing, backing up, or sharing resources and data. Storage hardware can be utilized traditionally and individually (DAS) or on a broader scale and collectively (SAN) within a network. Network storage plays a crucial role in modern data management, providing a wide array of advantages for businesses.
Network Infrastructure
Network infrastructure encompasses a set of hardware, software, and network policies that collectively facilitate the flow of data within a network. The interconnection of different components wirelessly or through network cables and fiber optics, or a mix of both, enables communication at varying scales. Common network infrastructure hardware includes routers, switches, access points, firewalls, and more.
Network security | Hardware
Hardware tools for network security serve as the frontline defense, safeguarding networks against unauthorized intrusion or access to sensitive data. These devices, operating independently from the OSI layer 1 to higher layers, each with distinctive features, are strategically positioned along the data flow and network traffic path, meticulously configured to ensure robust protection.
Network security | Software
The approach to safeguarding data against unauthorized access, with the assistance of diverse network security software, stands as a crucial step in network infrastructure configuration. Various types of security software tools, utilized to counter malware, viruses, spam, and unauthorized network entries, collectively establish an internal defense line within a network at the OSI layer 7.
Management and Monitoring
Network managers in all organizations, regardless of size, need a comprehensive network overview, real-time performance insights across all components, and proactive alerts for potential issues. Management software monitors resources network-wide, providing customized reports and flagging disruptions or anomalies in equipment performance to prevent problems.
Download Catalog
Download our catalog to explore a wide range of Dejpad products, services, and solutions. This catalog provides comprehensive details of our offerings and capabilities, giving you a precise insight into what we have to offer.

Cloud Computing
Providing various processing, storage, and data center management services based on cloud services eliminates the need to purchase, set up, and maintain physical equipment and internal servers.
Computing Solution
Integration, virtualization, intelligent automation of processing resources, and selecting the appropriate technology significantly boost computational power compared to traditional architecture.
Intelligent Data Storage
Intelligent data storage revolutionizes information management by optimizing storage resources, enhancing data accessibility, and ensuring efficient data retrieval. Leveraging advanced technologies like AI and automation, intelligent data storage solutions intelligently categorize and store data, enabling organizations to maximize data utilization, streamline operations, and bolster data security measures.
Data protection solutions
Data protection solutions are essential for safeguarding critical information against cyber threats, human errors, and equipment failures. These solutions provide effective organizational backup, persistent storage, and robust data protection, ensuring data integrity and security in the face of various risks.
Monitor, report, data analysis
Intelligent monitoring, reporting, and data analysis are pivotal components in modern data management strategies. By leveraging advanced technologies like AI and machine learning, organizations can proactively monitor their systems, generate insightful reports, and extract valuable insights from data.
Cybersecurity
Cybersecurity services protect digital assets from cyber threats through network security, threat detection, and incident response. By using advanced technologies and proactive measures, these services aim to prevent attacks and fortify data integrity against potential vulnerabilities.
"Cutting-edge infrastructure solution services"
In today’s business landscape, effective and secure communications hinge more than ever on robust network infrastructure. The performance of this network significantly impacts productivity, customer satisfaction, and overall business success. As a result, organizations striving for success in today’s competitive market prioritize investing in the most fitting network solutions, equipment, and services. With technology evolving swiftly, transitioning from traditional network setups is a smart move for companies. However, owing to the intricacies of new tech, selecting the right equipment and implementing efficient architectures has long been a top concern for tech managers. Additionally, having a round-the-clock support team in place to swiftly handle any complex disruptions that may arise is a strategic imperative.
Join us on the path to progress to leverage your network’s full potential and benefit from effective support. The expert technical team at Dejpaad Network Engineering and Security Company, adhering to global standards, will be there every step of the way – from requirement extraction to project design, proper execution, and round-the-clock support, standing alongside business owners.
- The architecture of traditional network infrastructures is not designed to secure modern organizational networks. To ensure the security of your business's data and network infrastructure, you require up-to-date software and hardware tools from reputable global manufacturers.
[Network solutions and network security]
In today’s interconnected world, people and businesses heavily depend on digital communications and online services. Yet, as cyber threats grow smarter, network security can’t rely solely on traditional security hardware and software. Embracing cutting-edge solutions with specialized equipment marks the initial stride in cybersecurity risk management and attack prevention. These solutions are offered across various categories at Dejpaad Company:

Equipment supply
As a trusted supplier, we manage the entire process from soliciting proposals, evaluating and selecting the most favorable bids, to facilitating bulk purchases.
Integrated solutions
Converged and hyper-converged solutions enable you to fulfill all your requirements using a unified system of hardware equipment, network infrastructure, and management software.
Desktop virtualization
Virtual Desktop Infrastructure (VDI) is a modern solution for managing and providing virtual access to desktops for users within organizations.
Data As a Service
DaaS, or "Data as a Service," is a cloud service model that enables organizations to utilize a cloud data service instead of locally managing and maintaining data storage infrastructures.
Backup
Data backup is a vital aspect of organizational system and information management. Backup solutions need to be precise, secure, and dependable to guarantee that no data is lost in the event of needing to swiftly recover data.
Disaster Prevention
Disaster prevention is a crucial aspect of risk management and information security. Effective strategies to avoid disasters necessitate preventive measures, meticulous planning, and responsive actions.
Disaster Recovery
Disaster Recovery solutions form a critical part of organizations' information security strategies. The primary aim of these solutions is to safeguard and promptly restore data and systems in the event of a disaster, such as natural calamities, human errors, or technological failures.
Software-defined everything (SDx)
Software-defined everything (SDx) represents a holistic approach in modern information technology, leveraging software to define and oversee the complete spectrum of a system or infrastructure. This versatile framework enables dynamic control, scalability, and efficiency across various IT components, revolutionizing the management and adaptability of digital systems.
Software-Defined Networking (SDN)
Software-Defined Networking (SDN) is a cutting-edge paradigm in the realm of networking, emphasizing the separation of network control and data planes. By centralizing network intelligence and programmatically managing network resources, SDN enhances agility, scalability, and network orchestration. This innovative approach streamlines network configuration, optimizes traffic flow, and facilitates the deployment of new services with unprecedented efficiency and flexibility.
Software-defined Storage (SDS)
Software-defined Storage (SDS) modernizes storage infrastructure by separating storage hardware from its management software. This strategy streamlines data storage, boosts flexibility, and cuts costs by enabling centralized, policy-driven control over storage resources independent of specific hardware configurations. SDS automates management tasks, simplifies storage operations, and optimizes resource utilization for enhanced scalability and efficiency.
software-defined wide area network (SD-WAN)
Software-defined Wide Area Network (SD-WAN) is a transformative networking approach that enhances connectivity and agility by separating networking hardware from its control mechanism. This technology optimizes network traffic, improves application performance, and simplifies network management through centralized control and automation, offering organizations greater flexibility and cost-effectiveness in managing their wide area networks.
Software-defined Infrastructure (SDI)
Software-defined Infrastructure (SDI) is a forward-looking concept reshaping how organizations manage and deploy their IT resources. By decoupling hardware from its management software, SDI enables centralized control and automation of compute, storage, and networking resources. This approach enhances flexibility, scalability, and efficiency, allowing businesses to adapt more swiftly to changing demands and optimize resource utilization. With SDI, organizations can streamline operations, improve agility, and reduce operational costs by dynamically adjusting infrastructure to meet evolving business needs.
Software Defined Compute (SDC)
Software Defined Compute (SDC) is a transformative approach that virtualizes and automates the management of computing resources. By separating the control of compute functions from the underlying hardware, SDC enhances flexibility, scalability, and efficiency in deploying and managing computational workloads. This technology enables dynamic allocation of processing power, streamlines resource utilization, and facilitates rapid adaptation to evolving business needs.
Hardening
Hardening involves fortifying system security through measures such as security configurations, software updates, service removal, and enhancing security settings to prevent diverse security threats.
Configuring security systems
Configuring security systems plays a crucial role in safeguarding organizational structures and information. For example, configuring Firewalls and UTM (Unified Threat Management) necessitates thorough security settings to effectively shield against diverse security threats.
Microsegmentation
Microsegmentation is a security strategy that involves dividing a network into smaller segments to enhance security by restricting communication between these segments. This approach provides granular control over network traffic, improves visibility, and strengthens overall network security by isolating different parts of the network from each other.
Zero Trust
Zero Trust is a security concept that operates on the assumption that organizations should not automatically trust any entity inside or outside their perimeter. This model requires strict identity verification for anyone trying to access resources on the network, regardless of their location. By continuously authenticating and authorizing devices and users, Zero Trust minimizes the risk of data breaches and unauthorized access.
Monitoring
Monitoring solutions are a crucial component of organizational security strategies, enabling the oversight of activities, behaviors, and diverse events within networks and information systems. By bolstering detection capabilities, facilitating rapid responses to security incidents, and enhancing overall network security, monitoring plays a key role in safeguarding organizational assets.
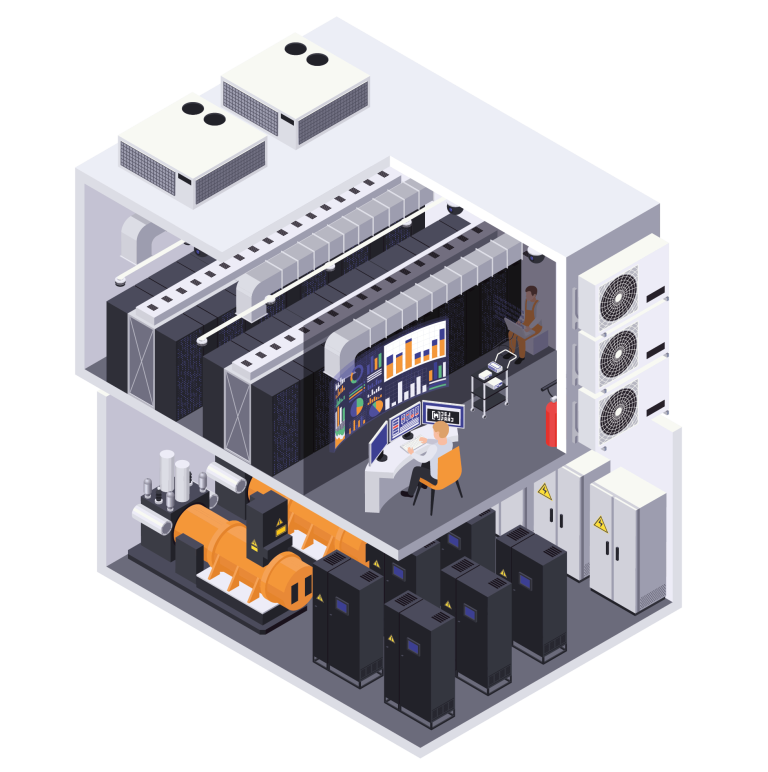
Data Center Infrastructure Management
Data Center Infrastructure Management (DCIM) is the management of tools and systems to monitor, measure, and control infrastructure components such as services, computers, networks, and storage devices in the data center.
Automation
This concept signifies the automation and automated execution of activities within systems and processes. Automation is deployed across diverse areas, such as information technology, manufacturing, organization, and process management.
